In the ever-evolving landscape of cybersecurity, ensuring optimal network security remains critical. The Juniper SRX Firewall stands out as a robust solution for organizations aiming to protect their critical assets. Renowned industry expert John Smith, a network security consultant, emphasizes, “Effective security is a continuous process, not a one-time setup.” This reflects the necessity of not only deploying the Juniper SRX Firewall but also maintaining and optimizing it over time.
Understanding the capabilities of the Juniper SRX Firewall can be a game-changer. Its advanced features help prevent unauthorized access and combat evolving threats. Yet, organizations often overlook regular updates and proper configuration. Security professionals should recognize that a firewall needs constant attention. A simple misconfiguration can leave vulnerabilities open, exposing the entire network.
Moreover, real-world scenarios highlight the importance of relying on expert advice. While many may think installing the Juniper SRX Firewall is the final step, continuous assessment is vital. Learning from previous incidents can lead to enhanced security measures. Creating an optimal strategy with the Juniper SRX Firewall involves persistence and awareness. Balancing proactive measures with a focus on ongoing evaluation can fortify network defenses significantly.

The Juniper SRX Firewall offers robust features that enhance network security. One key aspect is its integrated threat intelligence. This allows for real-time monitoring and analytics. It provides insights into potential threats. Users can take proactive measures against emerging vulnerabilities.
Another vital feature is the advanced policy controls. These enable fine-tuning of network access. Organizations can define user roles and set specific permissions. This granularity can prevent unauthorized access to sensitive information. However, complex configurations may lead to oversights. Regular audits are needed to ensure policies remain effective.
The SRX also supports automatic updates for its security definitions. This feature is crucial in a rapidly evolving threat landscape. Yet, relying solely on automation is not ideal. Human oversight is important. Teams should regularly review the updates to understand their implications. This balance between automation and manual checks enhances overall security posture.
Configuring a Juniper SRX Firewall requires a solid understanding of best practices to enhance network security. According to a recent industry report, 70% of security breaches happen due to misconfigured firewalls. Thus, paying attention to your configuration is essential. Always start with a clear network map. This will guide your policies and rules effectively.
Define zones accurately to segment traffic and minimize risks. Regularly updating firmware is crucial. Research shows that outdated software can lead to vulnerabilities. Ensure that your firewall receives automatic updates to address security flaws.
Implement strict access control lists (ACLs). Limit access based on necessity. Unused services should be disabled. This decreases attack surfaces, making it harder for threats to penetrate your network.
Monitoring traffic is often overlooked. Real-time analysis helps identify unusual patterns. A study revealed that 63% of organizations fail to look at logs regularly. Commit to a regular review cycle.
Track anomalies and address potential issues promptly. These proactive measures instill robustness in your network security. Not every configuration will be perfect; learning from challenges is part of the process. Reflect on your approaches, and iterate for improvement.
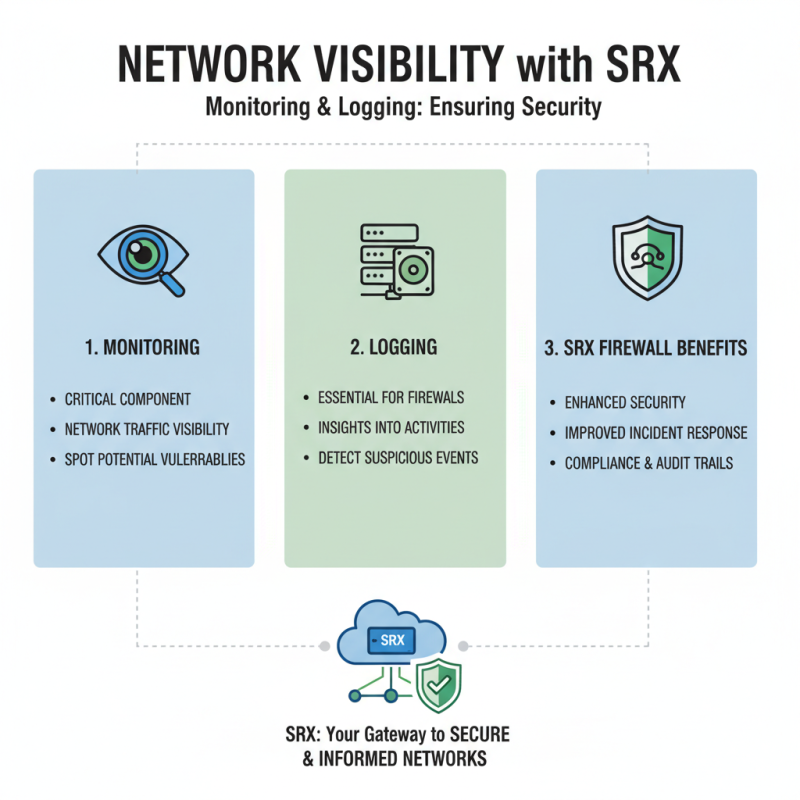
Monitoring and logging are critical components of network security. With any firewall, visibility into network traffic is essential. A well-configured firewall provides insights into potential vulnerabilities. Without proper logging, administrators may overlook suspicious activities.
Using effective logging settings, one can identify unusual traffic patterns. Adjust your log retention policy to retain data that matters. Real-time monitoring helps in responding to threats quickly. Alerts for abnormal events can be invaluable. However, too many alerts can lead to fatigue, causing important signals to be missed.
Consider integrating logging with advanced analysis tools. This could provide deeper insights into long-term trends. Regularly reviewing logs can help identify gaps in policies or configurations. Yet, it's crucial to strike a balance. Over-analyzing can also lead to confusion and delayed responses. Therefore, refining your approach to logging is vital for robust security management.
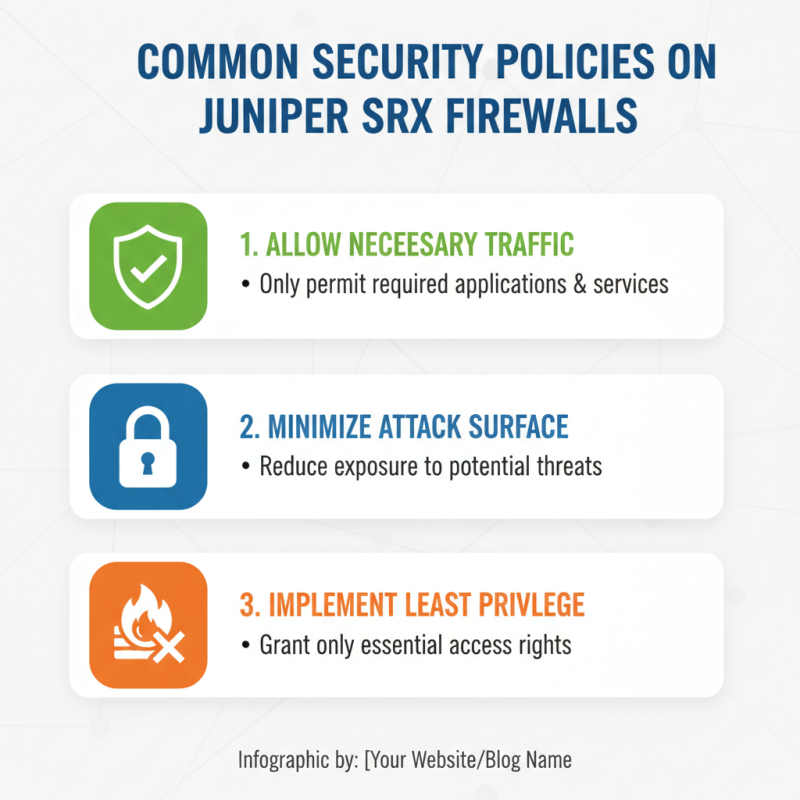
When configuring security policies on a firewall, it's crucial to define rules that align with your network's specific needs. One common policy is allowing only necessary traffic. For instance, if your organization relies on specific applications, you should only permit access to those services. This minimizes exposure to potential threats and reduces the attack surface.
Another essential policy involves defining zones for internal and external traffic. By segmenting the network, you can better control data flow and monitor suspicious activities. For example, traffic from the Internet should have stricter controls compared to internal communications. This zoning approach can reveal vulnerabilities and improve incident response times.
Regularly auditing these policies also matters. Sometimes, outdated rules remain in place, making networks vulnerable to attacks. Actively reviewing and adjusting policies helps maintain a secure environment. It’s a practice that many overlook but is vital for effective security management.
Maintaining your SRX firewall is crucial for optimal network security. Regular updates ensure that your firewall has the latest security features. Outdated firmware can expose your network to vulnerabilities. Schedule updates periodically and monitor for any critical patches.
Back up your configuration settings routinely. This simple step can save you time and headaches if something goes wrong. Store your backups in a secure location. Consider using automation tools to make this process smoother. Check your logs daily as well. They can provide insights into potential threats and help you understand patterns in your network traffic.
Regularly review user access controls. Ensure only authorized personnel have access to sensitive information. This not only boosts security but also reduces the risk of insider threats. Conduct audits on user activities. This practice can highlight any unusual behavior needing attention. Staying proactive is key to maintaining a secure firewall.